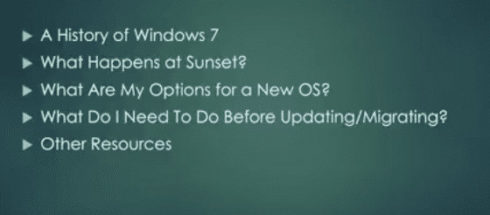
Windows 7 Is Being Sunset Within The Next 2 Years (Questions & Answers) Microsoft announced they are stopping mainstream support for Windows 7. Windows 7 is a popular operating system. So, this creates concern for many. Over time, the reliability and security of your computer will fade if you keep using Windows 7. So What […]